
DIGITAL HEALTH CHECK
Looking out for your business online?
We’ve been providing enterprises with high quality penetration testing since our inception, but we’ve been frustrated with how unobtainable industry standard testing is to small/medium sized businesses. To conquer this, we’ve distilled our enterprise testing down, and codified it into a bitesized digital penetration test, perfect for businesses who want to stay secure, but without the enterprise cost.
A MANUAL APPROACH
Our approach to testing is hands on. We aren’t offering automated scans; this is an expertise driven vehicle powered by our experience in large scale penetration testing.
If you’ve ever commissioned a security test only to receive a confusing checklist of issues instead of a report, this is for you.
AT YOUR OWN PACE
We formulate costs according to your risk. We know that company risk tolerance doesn’t scale with size – often small companies feel the need to accept more risk than is comfortable in order to operate profitably. Our offerings are based on your risk requirements, not your size. We don’t charge on the number of systems which need testing, but the time an attacker may spend on each system.
COVERING YOUR COMPANY
Cyber security can be expensive, often prohibitively. We believe everyone should have access to high quality cyber protection, no matter the size of their company. Our costing structure is designed to be proportional to the size and risk of your company’s infrastructure; becoming a proportional percentage of your infrastructural spending, not an unreachable cost.
WHAT IS A VETTED VULNERABILITY SCAN (and why you don’t want one).
Automated testing produces automated results. Often, suppliers will receive a list of every computer on a network, run each through an automated tool, and ‘vet’ any vulnerabilities that arise from it; weeding out false positives and false negatives. This is antithetical to a real-world environment. It causes more harm than good, especially to SMEs who may have penetration test requirements to bid for tenders, or apply for ISO
certifications. Often, what you receive is not a penetration test.
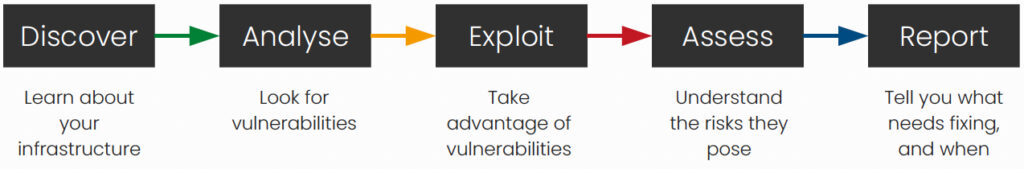
The digital health check is not a vetted vulnerability scan. We mirror what happens in the wild, as penetration testing should. Our framework is
simple:
AUTOMATED
INVALID AS A TENDER REQUIREMENT
NOT INFORMED BY EXPERTISE
NOT REPRESENTATIVE OF TRUE RISK
COST IS INFORMED BY INFRASTRUCTURE
MANUAL
COUNTS TOWARDS TENDER REQUIREMENTS
REPRESENTATIVE OF REAL WORLD
TESTS VULNERABILITIES TO ESTABLISH RISK
COST IS SCALABLE TO RISK APPETITE
The simple answer: our starting cost is £5,000, with testing running over the course of five days and a report issued to you on the sixth. This covers up to ten ‘parameters’.
BUT WHAT IS A PARAMETER (and what if you have more than ten?)
A parameter is anything that serves a purpose on your infrastructure. That could be a website, login portal, email server, or even a printer. Often, suppliers charge based on the number of IP addresses that exist on your network. This model is extremely wasteful, as unused IPs within your network will still be factored into final cost. We wanted a costing structure that better reflects your risk, not your size. As such, we calculate our costs based on the time it takes to attack a ‘parameter’, with an upper bound chosen by you. This reflects what you see in the real world – hackers dedicating a set amount of time to attacking a company before either succeeding, or giving up. Our hourly costs remain constant.





